The DarkSide ransomware has to allegedly shut down its operations after the threat actors lost access to servers and their cryptocurrency was transferred to an unknown wallet.
The DarkSide ransomware affiliate program responsible for the six-day outage at Colonial Pipeline. The crime gang announced it was closing up shop after its servers were seized and someone drained the cryptocurrency from an account the group uses to pay affiliates.
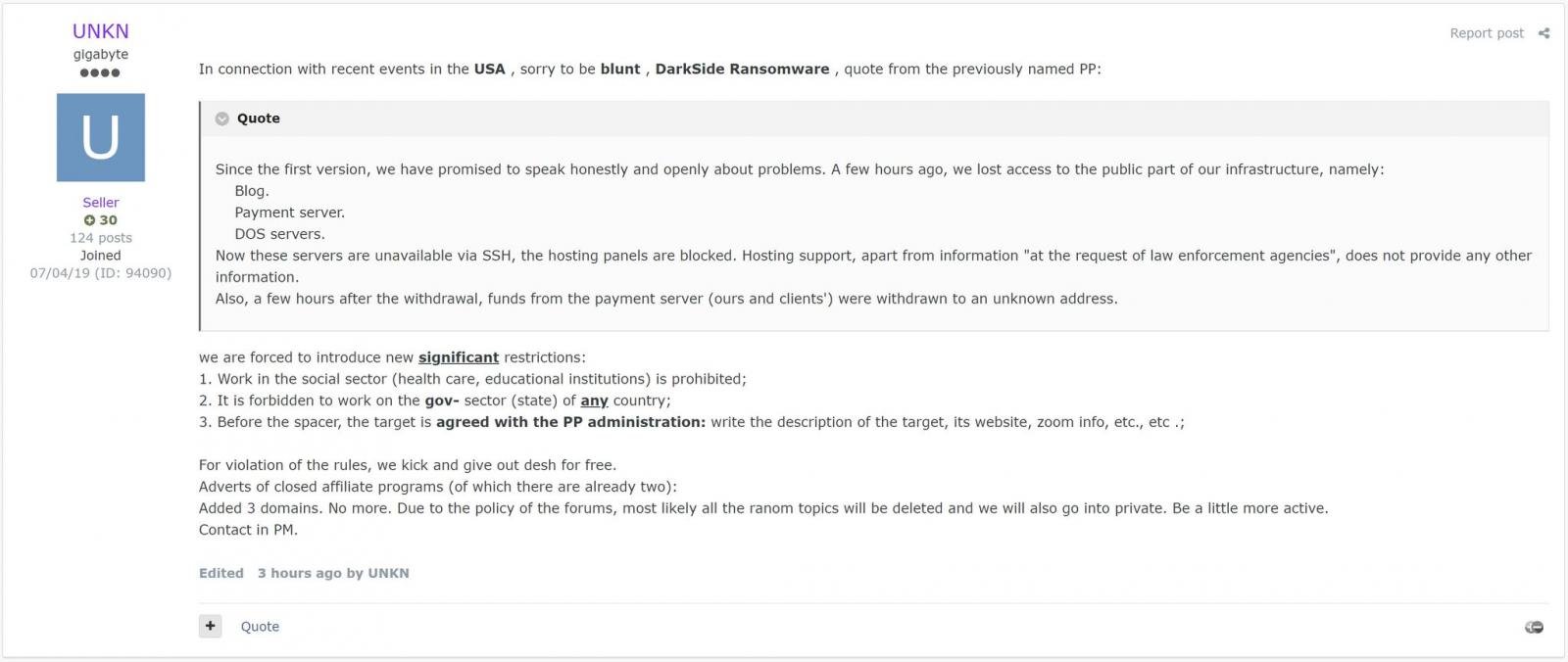
This news was shared by a threat actor known as ‘UNKN’, the public-facing representative of the rival REvil ransomware gang, in a forum post first discovered by Recorded Future researcher Dmitry Smilyanets on the Exploit hacking forum.
In the post, ‘Unkn’ shared a message allegedly from DarkSide explaining how the threat actors lost access to their public data leak site, payment servers, and CDN servers due to law enforcement action.
“Since the first version, we have promised to speak honestly and openly about problems. A few hours ago, we lost access to the public part of our infrastructure, namely : Blog, Payment server, DOS servers,” reads the forum post from UNKN.
“Now these servers are unavailable via SSH, the hosting panels are blocked. Hosting support, apart from information “at the request of law enfocement agencies”, does not provide any other information.”
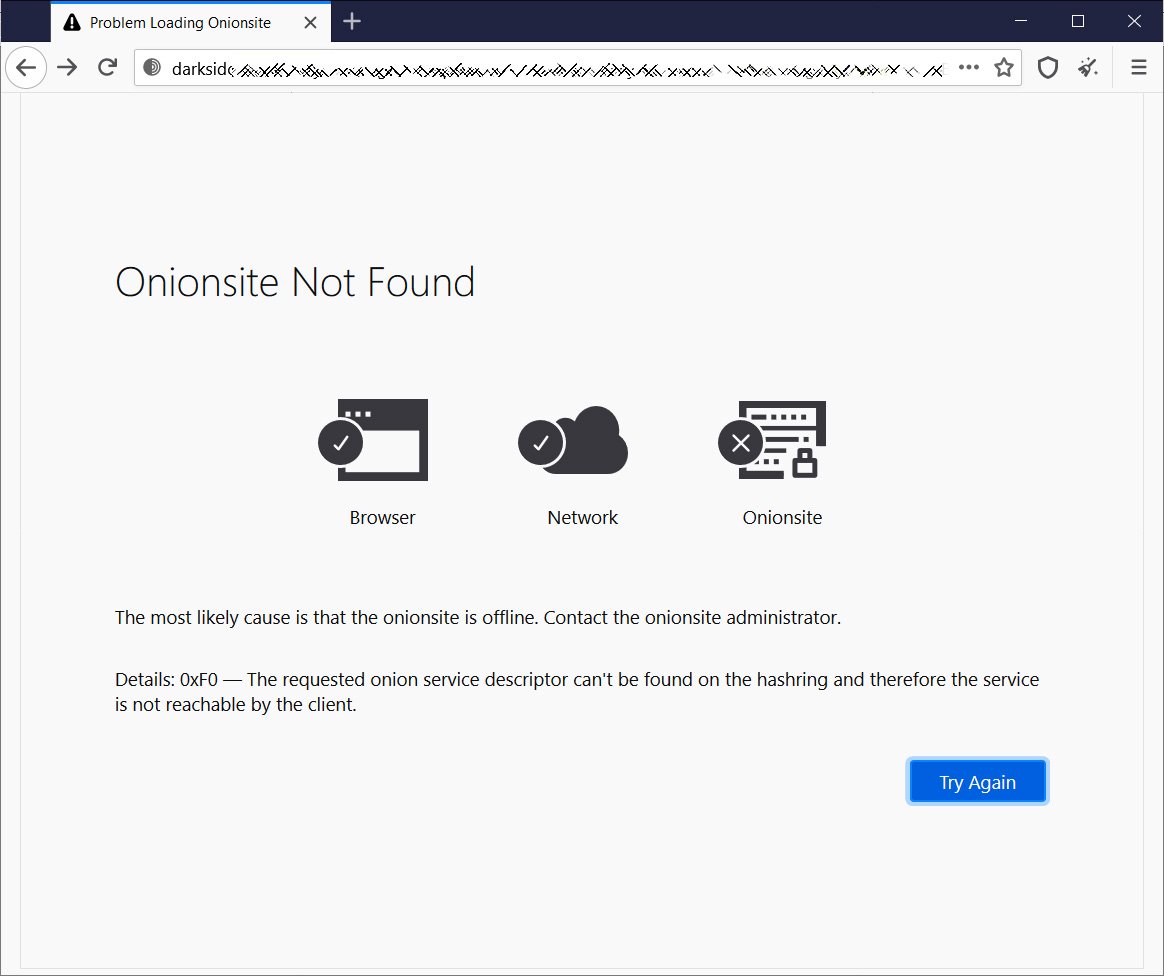
Starting yesterday, security researchers and journalists noted that the DarkSide data leak site was no longer accessible, and it was speculated that law enforcement had seized the server.
Starting yesterday, security researchers and journalists noted that the DarkSide data leak site was no longer accessible, and it was speculated that law enforcement had seized the server.
After pulling in $9.4 million in ransom payments this week between Brenntag and Colonial Pipeline, they may be stealing the money, so they do not have to pay affiliates and to blame it on a law enforcement operation.
DarkSide gang shut down the program
Intel471 gained access to the full message sent to affiliates of the DarkSide ransomware-as-a-service operation.
According to this message, DarkSide decided to close their operation “due to the pressure from the US” and after losing access to their public-facing servers.
Translated in English, the note reads:
Starting from version one, we promised to speak about problems honestly and openly. A couple of hours ago, we lost access to the public part of our infrastructure, in particular to the
blog
payment server
CDN servers
At the moment, these servers cannot be accessed via SSH, and the hosting panels have been blocked.
The hosting support service doesn’t provide any information except “at the request of law enforcement authorities.” In addition, a couple of hours after the seizure, funds from the payment server (belonging to us and our clients) were withdrawn to an unknown account.
The following actions will be taken to solve the current issue: You will be given decryption tools for all the companies that haven’t paid yet.
After that, you will be free to communicate with them wherever you want in any way you want. Contact the support service. We will withdraw the deposit to resolve the issues with all the affected users.
The approximate date of compensation is May 23 (due to the fact that the deposit is to be put on hold for 10 days on XSS).
In view of the above and due to the pressure from the US, the affiliate program is closed. Stay safe and good luck.
The landing page, servers, and other resources will be taken down within 48 hours.
An interesting point in this message is that the affiliates will be provided decryptors for their victims. These decryptors will allow the affiliates to extort those victims on their own without any affiliation with DarkSide.